
Explore the wireless world around you. Practical guides for SDR, WiFi pentesting, and open-source security hardware — buy it or build it yourself.
📡 Devices

PortaPack
Software-defined radio receiver and transmitter, 1 MHz to 6 GHz.

Biscuit
App-controlled WiFi and Bluetooth pentesting hardware.

RF Clown 2.0
Multi-protocol wireless testing and replay tool.
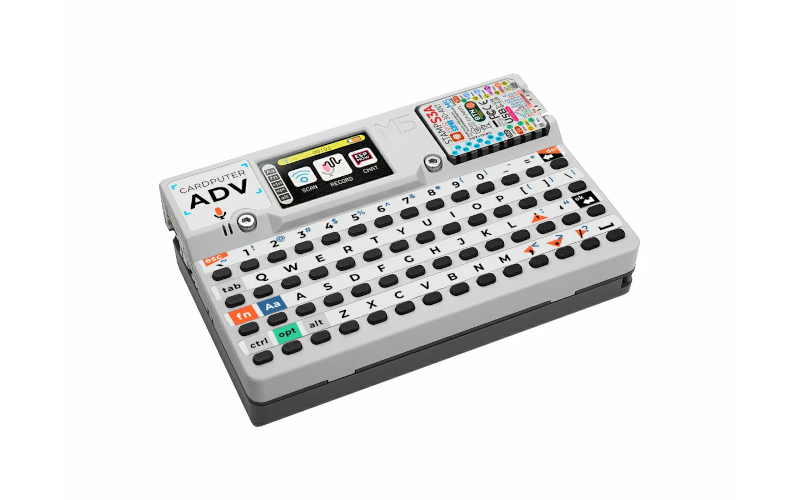
Cardputer ADV
Pocket-sized card computer for wireless hacking.

Shadow Apple
The Hak5 WiFi Pineapple clone.

Kali NetHunter Pro
Full Kali Linux on a phone.

Pwnagotchi
AI that learns to capture WiFi handshakes while you walk.
 CiferTech
CiferTech Civil Defense Engineer
Civil Defense Engineer DataSlayer Media
DataSlayer Media Evil M5 Project
Evil M5 Project Ghost Strats
Ghost Strats HaleHound07
HaleHound07 Ham Radio Crash Course
Ham Radio Crash Course Hedge Tech 95
Hedge Tech 95 Jeremiah o.A.T
Jeremiah o.A.T Just Call Me Koko
Just Call Me Koko KM6LYW
KM6LYW Man in the Mayhem
Man in the Mayhem Shuriken Hacks
Shuriken Hacks sn0ren
sn0ren Talking Sasquach
Talking Sasquach The Tech Prepper
The Tech Prepper Valley Tech Solutions
Valley Tech Solutions ZeekSec Labs
ZeekSec Labs